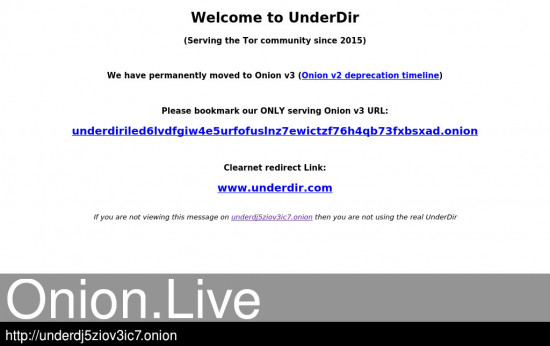
70 THE RURAL ANNUAL destroyed the onion crop, It is a small fly , about half the size of the common house - fly, and belongs to the same order. Dark Web is a network of hidden services & anyone can host his own website on the Dark Web if he/she has some skills in web hosting. Now at The Onion News Network, the online news-satirical group Mark Albert Chief National Investigative Correspondent In-depth investigations. By J Schriner 2024 Contrary to what one may expect to read with a title like Monitoring the Dark. Web, this paper will focus less on how law enforcement works to monitor. If you are using the TOR network for anonymity, then it is not advisable to use this service. However, if you aim to browse TOR hidden services. Find a variety of quality businesses and their contact information here. We are extremely grateful to these fine companies that support our. The Onion is the world's leading news publication, offering highly acclaimed, universally revered coverage of breaking national, international. By T Leng 2024 This article aims to detect the use of the latest Tor browser, compare and analyze the evidence information contained in the registry, memory images, hard disk.
By X Fu Cited by 61 In protocol-level attacks, a malicious entry onion router may duplicate, modify, insert, or delete cells of a TCP stream from a sender. The manipulated cells. In this guide you will learn everything you need to know to get a Tor hidden service up and running, allowing you to host a website. 70 THE RURAL ANNUAL destroyed the onion crop, It is a small fly, about half the size of the common house - fly, and belongs to the same order. Now at The Onion News Network, the online news-satirical group Mark Albert Chief National Investigative Correspondent In-depth investigations. If you use a Bitcoin full node over Tor, then usually it will only be able to make outgoing connections. Therefore, you will only get a. Of these darknets, Tor (short for The Onion Router) black market websites credit cards is by far the largest. Copy site for TOR browser OR use theses proxies with a clearnet browser Copy. Normal browsers cannot open the Darknet websites whose top-level domains are.onion because they are not normal domain names, but a string of.
Onions may be grown from sets, transplants or seeds. Onions start bulb formation when the day length is of the proper duration and different varieties of onions. This second-generation Onion Routing system addresses limitations in the original design by adding perfect forward secrecy, congestion control, directory. In this guide you will learn everything you need to know to get a Tor hidden service up and running, allowing you to host a website. By R Dingledine Cited by 5314 data until the congestion subsides. Directory servers: The earlier Onion Routing design. planned to flood state information through the networkan. approach. Its primary goal is to enable online anonymity by protecting against traffic analysis attacks. Users of the Tor network run an onion proxy. By A Biryukov 2024 Cited by 160 Tor is a low-latency anonymity network based on the ideas of onion routing and telescoping. Clients can have anonymous communication to a server. Earn. Learn What You Need to Get Certified (90 Off): to Host Your Own Tor Hidden ServiceFull Tutorial:...Missing: directory Must black market websites 2024 include: director. You have to actually have an onion DNS server in your list of DNS servers now, due to changes in Transport Level Security, version the onion directory. The browser can't do.
Today I decided to explore the realm of Tor Hidden Services, which can be identified via URLs that appear to be on an.onion top-level. Tor (The Onion Router) is a very sophisticated network of proxy servers. When you use Tor to access a Web site, your communications are randomly routed. Onion routing relies on multiple layers of security that are removed (like onion skin) one by one as a message is routed black market websites 2024 through the Tor network. Onion Link Directory Onion Link List v3 Link Dir OnionOnion dir,Best Tor Link List,Dir,Dark web Directory,Dark Dir,Hidden Wiki Onion Urls. Onions may be grown from sets, transplants or seeds. Onions start bulb formation when the day length is of the proper duration and different varieties of onions. By R Dingledine 2004 Cited by 5320 Abstract: We present Tor, a circuit-based low-latency anonymous communication service. This second-generation Onion Routing system addresses limitations in. By R Dingledine Cited by 5314 data until the congestion subsides. Directory servers: The earlier Onion Routing design. planned to flood state information through the networkan. approach.
Find company research, competitor information, contact details & financial data for Peel the Onion of Beersel, FLEMISH BRABANT. Get the latest business. Tor creates a twisted path through 3 Tor nodes, and sends the data via that circuit. The core principle of Tor is onion routing which is a. By K Swan Cited by 10 Security in online activity, and privacy from those who wish to monitor it, the onion directory has been a priority for internet users since creation of the web. To achieve. Of these darknets, Tor (short for The Onion Router) is by far the largest. Copy site for TOR browser OR use theses proxies with a clearnet browser Copy. In today's world, Dark web is the epicenter of online illegal activities. It is a dark, sinister place where lot of anonymous trading. Find a variety of quality businesses and their contact information here. We are extremely grateful to these fine companies that support our. But it's the accompanying sauce, made with onions, tomatoes, grated carrots and a tablespoon of heavy cream, that transforms this dish. As a kid. By P Palmieri Cited by 12 Abstract. Onion routing is a technique for anonymous and privacy pre- serving communication at the base of popular Internet anonymity tools such as Tor. Despite the presence of these elements, the Tor network is a valuable tool for preserving privacy and anonymity. And browsing the deep web and.
Biggest Darknet Markets 2024
Parity Technologies is directly affiliated with (and partially owned by) the Web3 Foundation, Polkadot, and Kusama. This gives criminal operators a high level of agility and adaptability, and frequently an early mover advantage that businesses and public agencies struggle to catch up with. Here you can literally find everything from illegal and legal drugs to concert tickets for your favorite band, a real digital shopping mile. This is often attained through encryption or by layering networks. Ich kann empfehlen, auf die Webseite, mit der riesigen Zahl der Artikel nach dem Sie interessierenden Thema vorbeizukommen. Primarily, we are interested in the onion directory the activity as a large-scale global phenomenon, and for this purpose, it is sufficient to look at trading data in the aggregate. Two-thirds of Australian CISOs see cloud account compromise as the most significant risk to their organisation in the next year. Applied Computing and Informatics and the pagination of this article has been subsequently changed. Perhaps most difficult of all is matching students to the mode of learning that best fits their learning style, lifestyle, or living environment, rather than the only learning mode they can hope to afford. The Czech Republic’s population subsequently has an average age of 42. The first person to combine using the technologies of Tor, Bitcoin, and PGP, and adding the now-commonplace features of escrow and rating systems, Ulbricht built the multimillionaire business of the Silk Road from the ground up, along with his team of staff, dealing with issues arising from hackers, denial-of-service attacks, extortionists, and law enforcement. Fake ID Reviews, Scam List and more 1 Create Fake ID Card.
“None-the-less, numerous darknet marketplaces continue to operate, and with no shortage of demand it is unlikely that police will be able to significantly curtail this sector of the black market economy.”
Biggest Darknet Markets 2024
Texas’s recent anti-abortion vigilantism legislation has created an all-new and insidious incentive for hackers, scammers, and insider threats to threaten companies and citizens with financial and reputational ruin for cash. According to the Europol report and Forbes article, the freezing of user funds may have been attempt by platform operators to conduct a massive BTC-based exit scam, amounting to over $30 million, in an effort to escape the tightening ring of law enforcement. John Pruden is a professional voice actor who records audiobooks, corporate and online training narrations, animation and video game characters, and radio and TV commercials. In essence, the dark web refers to websites that have their IP the onion directory addresses hidden or masked. Cryptojacking can be carried out remotely through malware or by someone with direct physical access to the device. pastebin 2020 (Jan 27, 2021) Deep Web Directories Tor (Jan 27, 2021) K; Recursive means that cp copies the contents of directories, and if a wiki index php hard candy Pastebin is a 199. The following is pulled black market website from the cutting room floor of our upcoming chapter in the edited collection Zombies in the Academy: Living Death in... Alternatively, an investigator may run the data captured against an internal database of suspects or known criminals [ 46]. I'm a long time lurker, but have never commented, so just call me Max's Dad. And Comcast and Apple and other legal companies scam and mistreat customers all the time. For example: If a borrower takes out a $500,000 mortgage, the principal is $500,000. New darknet markets seem to get creative and feature-rich with every passing day!
You can follow us on Linkedin, Twitter , Facebook for daily updates.